MARSHALL PENFIELD in front of a large group of graduate
students -- lecturing. Charlie quietly slips in the back.
MARSHALL
From set theory's inception, some
have argued it's a game that
includes elements of fantasy.
Wittgenstein questioned how
Zermelo-Fraenkel set theory handled
infinities. Errett Bishop dismissed
it as "God's mathematics, which we
should leave for God to do."
Marshall spies Charlie in the back.
MARSHALL (cont'd)
Next week's talk will be on the
Spectral Theory of non-Hermitian
Random Matrices. Thank you.
The students file out. Charlie approaches.
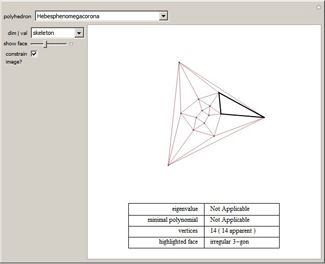
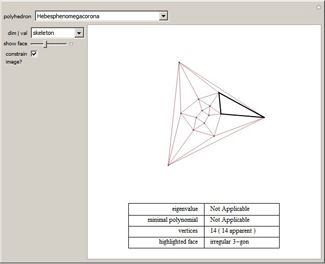
Each
eigenvalue in the
spectrum of a combinatorial graph's
adjacency matrix gives rise to a "spectral realization" of the graph. Such a realization is both eigenic (replacing each vertex with the vector sum of its neighbors is equivalent to scaling the figure) and harmonious (each automorphism of the graph is realized by an isometry of the figure). In many cases, they are also just plain fascinating. This Demonstration reveals the spectral realizations of (the skeleton of) each named polyhedron in
Mathematica's
PolyhedronData[] collection.
AMITA
What if it's not just computer code
... but a cipher code?
MARSHALL
If it is, could take months to
figure out.
NIKKI
They painted this on a wall -- I
doubt they made it hard to crack.
CHARLIE
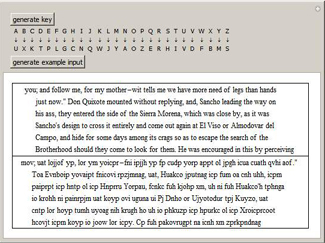
Maybe a simple Vigenere cipher?
MARSHALL
With the first 13 alphabet letters
matched to these 13 code symbols --
AMITA
And the key word is "Vanguard"--
Amita brings up a Vigenere software program on a second
screen -- and it translates the computer code into TEXT.
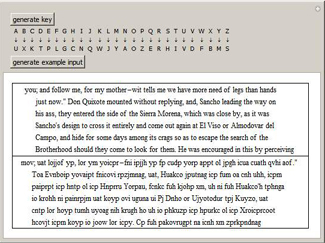
Substitution ciphers are one of the simplest forms of encryption, where replacement rules are provided that map each letter of the alphabet onto a different letter. This tool will generate randomly chosen keys that map the 26 letters of the English alphabet onto themselves. It also generates snippets of sample text from a range of English sources.